In the trendy digital age, the need for secure and personal facts sharing has never been greater crucial. With the increasing risks of statistics breaches and unauthorized access, people and organizations are in search of reliable solutions to proportion touchy data without compromising their privacy. This is where ZeroBin comes into play.
In this comprehensive manual, we can discover what ZeroBin is, how it works, and its blessings, and additionally delve into a number of the exquisite options to be had in the market. Whether you are a man or woman seeking to percentage private statistics or a crew taking part in touchy tasks, this guide will assist you in making informed selections to make sure your information stays stable.
Understanding ZeroBin:
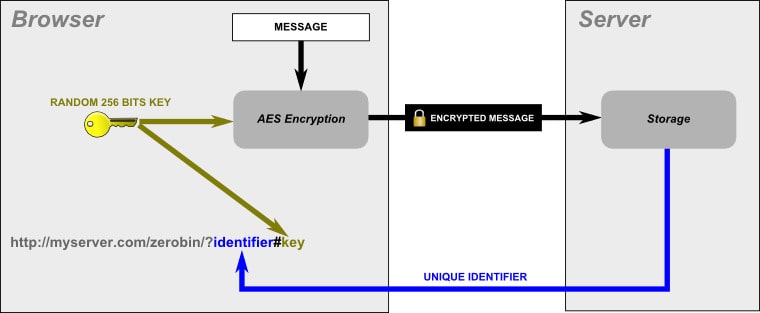
ZeroBin is a web-based open-source utility designed to facilitate secure statistics sharing. Unlike traditional platforms that would disclose your records to potential risks, Zero Bin makes a specialty of encryption and personal privacy. When you submit a chunk of textual content to Zero Bin, the software encrypts the content material at once inside your browser earlier than storing it on the server.
This encrypted content can best be accessed and decrypted with the aid of someone with a unique URL generated throughout the sharing technique. This method guarantees that even if the facts are saved on a server, they remain encrypted and inaccessible to unauthorized events.
Advantages of Using ZeroBin:
The advantages of using Zero Bin are compelling, making it an excellent preference for the ones involved in information security and privateness:
1. Data Encryption and Security: ZeroBin’s central characteristic is its robust emphasis on information encryption. Encrypting the facts on the supply ensures that even though the information is intercepted throughout transmission or stored on a server, it stays unreadable without the decryption key.
2. User Anonymity and Privacy: Unlike some structures that require user identification, Zero Bin does not ask for any personal information. This ensures that your information-sharing activities continue to be nameless, offering an added layer of privacy.
3. Ease of Use and Accessibility: Zero Bin boasts a person-pleasant interface, making it smooth for each sharer and recipient to navigate the platform. Additionally, it may be accessed from numerous gadgets, taking into account flexibility in sharing facts securely.
4. Collaboration Capabilities: For groups operating on personal tasks, ZeroBin offers collaboration features. This permits a couple of users to get admission to and contribute to shared content material securely, enhancing productiveness without compromising protection.
Exploring Alternatives to ZeroBin:
While Zero Bin is a first-rate choice, it is crucial to remember other options that could better shape your unique needs:
1. Pastebin: Pastebin is a famous platform for sharing text snippets quickly. However, it lacks the robust encryption capabilities of ZeroBin, making it much less suitable for sharing particularly touchy records.
2. PrivateBin: PrivateBin is a direct opportunity to Zero Bin, focusing on secure facts sharing. It offers comparable encryption capabilities, permitting customers to percentage data privately.
3. CryptPad: CryptPad takes secure sharing to the subsequent degree by enabling collaborative editing of diverse types of files, which include textual content files, presentations, and more. This makes it an incredible desire for groups operating on projects that require more than simply easy textual content sharing.
How to Use ZeroBin Effectively:
Using Zero Bin successfully is a straightforward process. Here’s a step-by-step manual:
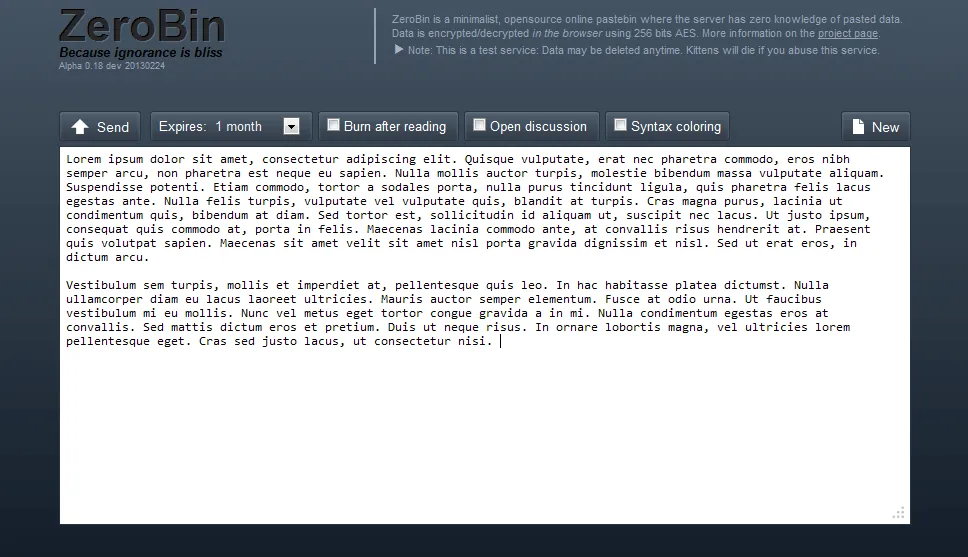
1. Access the ZeroBin Website: Start by gaining access to the ZeroBin website through the usage of your chosen web browser.
2. Enter Your Text Snippet: In the specified location, enter the textual content snippet that you need to share securely.
3. Set Optional Security Measures: You have the choice to beautify safety by setting an expiration time for the content material or including a password. These measures make certain that even though the URL is accessed later, the content material stays stable.
4. Generate the Unique URL: Once you have entered the text and any non-compulsory protection settings, click the ‘Submit’ button. This action generates a unique URL that corresponds to the encrypted content material.
5. Share the URL: Share the generated URL with the supposed recipient via a steady communication channel. The recipient can get admission to the content material by clicking on the URL.
Factors to Consider When Choosing an Encrypted Data-Sharing Tool:
When selecting the proper encrypted information-sharing device in your desires, recall the subsequent factors:
1. Security Features: Look for gear that offers end-to-quit encryption and a zero-know-how structure, making sure that only authorized events can get the right of entry to the content.
2. Customization Options: Some gear permits you to set expiration dates or add password safety to enhance protection.
3. Collaboration Features: If you’re operating with a team, recollect gear like CryptPad that helps collaborative modification of documents while keeping encryption.
4. User-Friendliness: Choose an easy device to use both for you and the recipients of your shared content material.
5. Mobile Accessibility: Ensure that the device features nicely on various devices, allowing for seamless sharing and admission from smartphones and capsules.
Additional Tips for Secure Data Sharing:
- Use Strong Passwords: When the use of gear that offers password safety, continually use strong and unique passwords. Avoid the use of without problems guessable passwords or reusing passwords from other bills.
- Be Cautious with Expiration Times: While setting expiration instances for shared content material can enhance security, be cautious not to set them too quickly. Ensure that recipients have sufficient time to get entry to the content material earlier than it expires.
- Share URLs Privately: When sharing the URLs generated by using secure information-sharing gear, achieve this through private and secure communique channels. Avoid sharing URLs on public platforms or through unencrypted email.
- Regularly Update and Patch: If you’re the usage of self-hosted solutions or open-source tools, make sure to hold them up to date with cutting-edge protection patches to save you vulnerabilities.
- Verify the Source: When the usage of online tools, always ensure you’re gaining access to a legitimate website. Phishing attacks may want to lead you to fake websites designed to scouse borrow your statistics.
- Educate Recipients: If you are sharing facts with others, train them on the importance of stable information coping. Make certain they apprehend the need for the usage of robust passwords and follow protection fine practices.
- Use Two-Factor Authentication (2FA): Whenever viable, enable two-issue authentication on systems that offer it. This adds an extra layer of protection for your debts.
Additional Resources:
- ZeroBin Official Website: Visit the official ZeroBin website for more records about the tool, its functions, and utilization instructions.
- PrivateBin: Learn extra approximately PrivateBin, an alternative to Zero Bin, which makes a specialty of stable records sharing with encryption.
- CryptPad: Explore CryptPad, a collaborative online editor that gives encryption for diverse forms of files, presentations, and more.
- How Encryption Works: A knowledge guide of how encryption works and why it’s critical for data safety.
- Choosing a Password Manager: If you are the usage of password-protected gear, don’t forget the use a reliable password manager to store and generate robust passwords.
- Cybersecurity Best Practices: The United States Computer Emergency Readiness Team affords numerous cybersecurity guidelines and assets for people and companies.
- StaySafeOnline: A complete aid for online protection, presenting data approximately cybersecurity, privacy, and pleasant practices.
Conclusion:
In a global wherein information safety and privacy are paramount, tools like ZeroBin provide a dependable answer for sharing sensitive statistics without compromising confidentiality. Its encryption abilities, personal anonymity, and collaboration features make it a standout desire. However, bear in mind to explore options such as Pastebin, PrivateBin, and CryptPad to determine the great fit for your unique necessities. By prioritizing stable statistics sharing, you contribute to a more secure online environment while safeguarding your valuable statistics. Whether you’re a person or a part of a crew, the right encrypted facts-sharing device can make all the difference in preserving your facts secure.
Frequently Asked Questions (FAQs):
Q1: What is ZeroBin?
Ans: ZeroBin is an internet-primarily based open-source software designed for steady information sharing. It encrypts statistics inside the person’s browser before storing them on a server. Recipients can then get admission to and decrypt the data using a unique URL, ensuring the privacy of shared records.
Q2: How does Zero Bin make certain security?
Ans: Zero Bin employs patron-facet encryption, meaning the records are encrypted earlier than they leave your browser. This encrypted record is saved on the server, but only users with a unique URL can decrypt and access it. This method ensures that even if the server is compromised, the information stays unreadable.
Q3: What are the advantages of the usage of ZeroBin?
Ans: ZeroBin gives information encryption, consumer anonymity, ease of use, and collaboration competencies. It safeguards your shared data from unauthorized access and provides a steady platform for touchy data sharing.
Q4: Can I use Zero Bin for collaborative work?
Ans: Yes, Zero Bin supports collaboration. Multiple customers can get entry to and contribute to shared content securely, making it an appropriate option for teams running on private tasks.
Q5: Are there alternatives to ZeroBin?
Ans: Yes, there are alternatives to ZeroBin. Some options consist of Pastebin (much less targeted on encryption), PrivateBin (similar to Zero Bin), and CryptPad (which helps collaborative editing with encryption).
Q6: How do I make certain my shared content material is stable?
Ans: Use sturdy passwords, proportion URLs privately, and recollect placing expiration instances for content. Educate recipients about safety practices and avoid sharing sensitive facts through unsecured channels.
Q7: Can I accept it as true with self-hosted or open-supply answers like ZeroBin?
Ans: Self-hosted and open-supply solutions can be steady if nicely carried out and frequently up to date with protection patches. Make positive to observe high-quality practices for server protection in case you pick to self-host.
Q8: What is encryption, and why is it crucial?
Ans: Encryption is the technique of changing data right into a code to prevent unauthorized get admission to. It’s important for defensive sensitive information at some point of transmission and storage, ensuring that even if the information is intercepted, it remains unreadable without the decryption key.
Q9: How do I select the right encrypted information-sharing tool?
Ans: Consider elements like safety capabilities, customization options, collaboration competencies, person-friendliness, and cellular accessibility. Assess your particular needs and choose a tool that aligns with them.
Q10: Can I use Zero Bin on cellular gadgets?
Ans: Yes, ZeroBin is on the market for numerous gadgets, including mobile telephones and pills. This flexibility allows you to securely proportion facts irrespective of the device you are the usage of.
Read More: Top 10 Similar Sites Like Call2Friends and Their Alternatives